| Authentication mechanism to login to SQL Server database engine is either Windows authentication or SQL Server account. Sometimes you will face authentication issues with database portability, example when you migrate a database from one SQL Server instance to another SQL Server instance, DBA has to ensure that all logins in Source SQL Server instance is existed on the target SQL Server instance. Organisations often experience these problems during failover when using database mirroring. |  |
SQL Server 2012 addresses these authentication and login dependency challenges by introducing Contained Database authentication to enhance authorization and portability of user databases.
What is Contained Database Authentication?
Contained Database Authentication allows users to be authenticate directly into a user database without logins that reside in database engine. It allows authentication without logins for both SQL users with passwords and windows authentication without login. It is a great feature when you want to implement AlwaysOn Availability Groups.
Enabling Contained Databases
Contained Databases is a property which you can enable or disable via the Advanced Properties page in SQL Server Management Studio or with T-SQL
Enable Contained Database Authentication using SQL server Management Studio
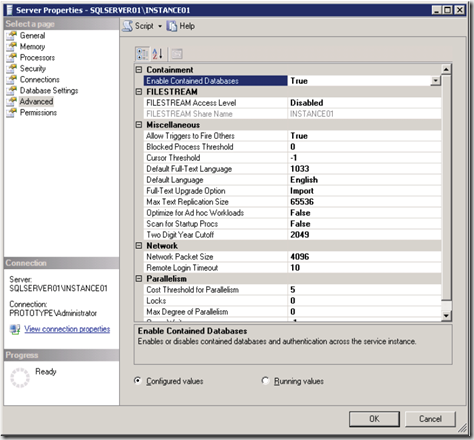
1. In Object explorer, right-click a SQL Server instance, and then click properties
2. Select the Advanced page, and in the Containment section , set the property Contained Database to true and then click OK.
Enable Contained Database Authentication using T-SQL
1: sp_configure 'show advanced options' 1,
2: Go
3: sp_configure 'Contained database authentication', 1;
4: Go
5: RECONFIGURE;
6: GO
Creating Users
If user does not have a login in master database, the connection string must include the contained database as initial catalog. The below T-SQL can be used to create a contained database user with a password.
1: CREATE User KennyB
2: WITH PASSWORD = '2e4ZK933'
3: ,DEFAULT_LANGUAGE = [ENGLISH]
4: ,DEFAULT_SCHEMA = [dbo]
5: GO
To migrate the SQL Server authentication login to contained database user with a password then you can use below T-SQL
1: sp_migrate_user_to_contained
2: @username = N '<User Name>',
3: @rename = N 'keep_name',
4: @disablelogin = N 'do_not_disable_login';
5: GO
Contained Database Authentication Security Concerns
Without knowledge of DBA, user can create and grant database users in contained database if user has ALTER ANY USER permission.If user gains the access to a database via contained database authentication then user has potential to access other databases within the database engine if these databases has the guest account enabled.
| Share this post : |  |
 |
 |
 |
 |