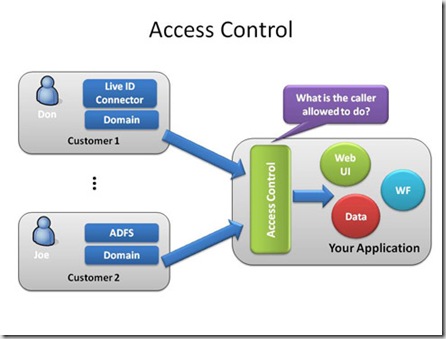
My previous article explained the basics of building windows azure services. Let’s start looking at the .NET Access Control Service. .NET Access Control Service allows you to use the authentication and authorization services from external sources that are maintained by security experts. Security experts control the authentication and issue the token to the application. Application just uses those tokens by avoiding the authentication process.
The Microsoft .NET Access Control Service is a centralized cloud-based service which acts as an identity provider but it also provides some additional services like it rely on existing identity providers such as WLID and the Geneva which supports the standard federation protocols.
The main responsibility of the .NET Access Control Services is to provide a set of identity tokens used by your application. It act as configurable engine in cloud environment.
Advantages
The Microsoft .NET Access Control Service helps you to avoid complicated programming for building secured applications. Using Declarative model you can simply configure your application. Simplified coding and rule-based authorization are features of this service.
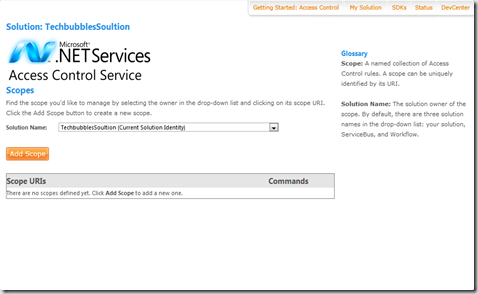
Configuring a Access Control Service
You can configure the .NET Access Control Service through the administration portal. You will see the set of solution names under drop-down which represents the owners for various scopes
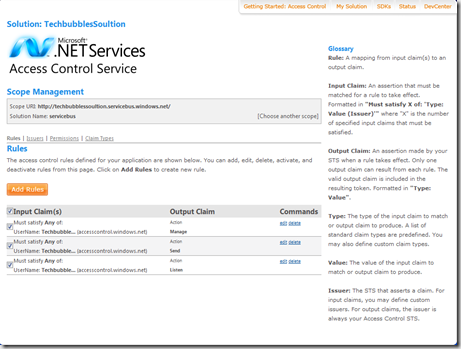
 Scope is collection of rules and you can define the rules as follows
Scope is collection of rules and you can define the rules as follows
Every solution comes preconfigured with a set of access control rules for bot the .NET Service Bus and the .NET Workflow Service.
To summarize the functionality.
- Define the scope for your service
- Define necessary rules to produce the claims expected by your service.
- In your service logic you will need to write code to inspect the incoming claims and make authorization decisions.
You can also read the following article about .NET Service Bus
Source for the content in the post is MSDN May magazine.